Lets Review the flavors of HEES which includes Sub-Lex and HESS now just referred to as the High Entropy Encoding Systems family .
This is an expansion of our Substack post the reader may want to review that https://open.substack.com/pub/michele211/p/high-entropy-encoding-as-a-new-standard?utm_campaign=post-expanded-share&utm_medium=post%20viewer
When we first conceived of HESS we mentioned we expected there to be variants based on what we saw as a new standard of encoding in this Article we introduce HESS 4 the first symbol less encoding systems.
Sub-Lex (HESS 1) a zero relationship encoding
Sub-Lex is the original and most developed implementation of the High Entropy Encoding Systems (HEES) framework. It demonstrates how positional encoding, drifted vector maps, and seeded character sets can be used to layer messages within natural or artificial narratives.
While this paper focuses on Sub-Lex’s technical implementation, the conceptual foundation of Sub-Lex—particularly its vector-based structure and post-symbolic design—is explored more broadly in other works, including the paper Beyond Natural Languages (Cannon, 2025) and accompanying technical articles. These works define HEES as a post-quantum framework for encoding messages in a way that preserves entropy, even in the presence of shared relational context.
In the sections that follow, we describe the evolution of Sub-Lex through its first two major versions, each of which balances message security, entropy retention, and plausible deniability through different architectural trade-offs.
Sub-Lex 2 (HESS 2) : Drifted Encodings and Entangled Instructional Systems
The second generation of Sub-Lex abandons natural language narratives entirely in favor of a purely data-driven representation, using an internally randomized hexadecimal charset. A seed key S is used to:
- Randomize the full hex charset Σ₁₆ = {0–F}, producing Σ₁₆′
- Randomize the numeric subset Σ₁₀ = {0–9}, producing Σ₁₀′
- Generate a deterministic drift function fₛ(i) as in Version 1
The encoded message becomes a sequence of indices into Σ₁₆′, making the output indistinguishable from noise. These values may be transmitted inside innocuous data fields or embedded into metadata.
A refinement of this version integrates with the Matrix protocol, leveraging its double ratchet mechanism to cause messages to expire and become unrecoverable. Without access to the original seed S, the drift function, and both randomized charsets, message reconstruction is computationally infeasible.
This version introduces a significant philosophical shift:
The message is no longer treated as content, but as an instruction set for rebuilding the system that generated it.
In effect, the encoded message becomes a non-symbolic entangled state, whose meaning cannot be localized to any single component.
Brute-force attacks yield a superposition of plausible results, similar to token prediction in large language models. HEES encodings resist deterministic cracking precisely because they do not adhere to symbolic mappings.
HESS 2 has uses beyond emulating encryption or protecting medical records. Its internal character set is typically a modified base-16 Sub-Lex, but it can also use base-26 NLS, and even scale to much larger charsets—such as the building blocks of JSON.
This eliminates the need for serialization and deserialization in message transmission. The message becomes a signal, like messenger RNA in human genetics:
The signal is not the message. The signal is the instructions to build the message.
This may form the basis of a future AI-to-AI language.
HEES Version 3 Generative
Version 3 introduces a generative workflow for embedding private messages within public narratives. Unlike earlier Sub-Lex systems, HEES 3 emphasizes entropy modeling, narrative shaping, and optional reuse of keys.
This version moves away from tracking vectors of characters to creating a predictive mapped space , using ML model the system determines the most optimized map to arrange the message within the narrative.
The experience follows one of two flows: New Mapping or Existing Mapping.
New Mapping Mode
In New Mapping Mode, the user begins with a blank slate. The assistant guides the process step by step.
The user first enters the message to be encoded — typically up to 120 characters. For a 600-character post, using around 20% of the mapped space is ideal to maintain plausible entropy.
Next, the user provides a prompt describing the visible, public-facing topic of the post. This guides the assistant in shaping a coherent and plausible narrative while concealing the payload.
The assistant then performs mapping optimization, distributing the message characters across the available positions in a way that minimizes detectable patterns while preserving linguistic coherence.
At this stage, the user may optionally engage in scrambling — manually shifting or shuffling characters like a word puzzle to further obscure any surface regularities. The assistant adapts the narrative in real time to reflect these changes.
Once mapping is finalized, the assistant generates the full narrative. This output respects the payload map, incorporates the user’s public topic, and applies entropy and grammatical shaping to maintain naturalism.
The assistant then highlights the embedded characters, allowing the user to inspect and confirm proper alignment. Any misalignments caused by hallucination or drift can be corrected before finalization.
After user approval, the assistant inserts two special marker characters representing a 4-digit drift value. This value introduces controlled randomness into the mapping — acting as a noise vector to reduce correlation risks and obfuscate structure.
Finally, a cryptographic key is generated. This includes the drift value, character position mapping, any scramble transformations, and a checksum of the final output. The key, typically 128 or 256 bytes, can be saved, exported, or reused for future decoding.
Existing Mapping Mode
In Existing Mapping Mode, the user starts with a previously generated key.
Upon input, the assistant reconstructs the original character map and displays the locked positions.
From there, a new narrative is generated — this time constrained by the fixed mapping. The user can choose a new public prompt or reuse the original, but the payload positions remain immutable unless explicitly unlocked.
If the user chooses to override specific positions for creative or flow reasons, a new key is generated to reflect the change. This ensures that the immutability of the original message structure is preserved and verifiable.
Reuse and Longevity
- Reused across multiple posts
- Regenerated with small variations
- Stored indefinitely if securely kept
While the entropy profile remains constant, the visible narrative can evolve. The drift value ensures each reuse appears unique at the surface level.
Optional Sub-Lex Layering
- Sub-Lex for compact vector-encoded secrets
- NLS for narrative-shaped embeddings of larger messages or data fields
This dual-mode approach increases flexibility and preserves forward compatibility with future Sub-Lex interpreters.
HEES Version 4 The first symbol less encoding.
HEES Version 4 marks a major leap in the evolution of high-entropy language systems. It preserves the predictive mapped-space architecture introduced in HEES 3 but eliminates one of the last remaining dependencies: surface symbols.
Where earlier versions required the generation of a narrative containing embedded characters or symbols to carry the hidden message, HEES 4 discards that requirement entirely. The narrative is now used only as a spatial placeholder — a container to define the available 600-character mapped vector space, rather than a carrier of any visible payload. This removes all constraints on the narrative’s wording and allows the message-layer to exist in pure vector space, independent of text content.
HEES 4 also retains the external character set mapping architecture pioneered in HEES 2, allowing mappings to be non-sequential and seeded. Character sequences in the original message are transformed via deterministic offsets, masking predictable distribution and increasing resistance to pattern analysis. The message is no longer tied to literal letters in the narrative — instead, it is defined solely by position.
By removing all requirements to modify or regenerate the public narrative, HEES 4 offers a vastly improved user experience. Creators can now write or select any post — even one written weeks earlier — and layer a private message within its structure without changing a single visible word. This opens the door to retrospective layering, message re-keying, and a host of AI-free workflows for encoding, previewing, and verifying message presence.
For analysts or adversaries, the result is indistinguishable from ordinary text — no visible symbols, no irregular phrasing, no embedded tokens. The message layer exists purely in structure: a phantom of position, not presence.
The Death of Symbology
Traditional cryptography and steganography rely on the presence of “symbols”whether those are flipped bits in an image or ciphertext characters in a string.
-
The “Zero-Symbol” Breakthrough: By using an internally mapped character set in a 600-character bounded space, HEES 4 is not hiding a it’s translating a spatial relationship.
-
Not Steganography: Steganography is the act of hiding data inside another object. In HEES v4, the “carrier” text is not a container; it is a geographical map. If an attacker analyzes the text, they see a perfect statistical match for natural language because the text itself has never been modified.
The Semantic Layer Extraction
Framing as “translating from a low-entropy language to a high-entropy semantic layer” matches the 2026 academic focus on G Theory (Semantic Generalization of Shannon’s Theory).
-
The Efficiency Moat: Humans assign meaning to words through an “Information Bottleneck”. HEES system exploit this by mapping high-entropy “latent” information into the naturally occurring low-entropy “valleys” of human speech.
-
Many-Worlds Defense: Because the mapping is internal and bounded, a brute-force attack on the 600-character space would yield a “probability cloud” of equally valid semantic results. Without the specific vector-handshake, it is mathematically impossible to distinguish a “true” message from the background noise of the internal character set.
IP and Operational Implications
By removing all “symbology,” we have created a system that is Detection-Proof rather than just Encryption-Hard.
-
Systemic Safety: Like the HardBound architectural model, which uses disjoint shadow space for metadata to ensure memory safety, your internal character set exists in a “shadow” layer that is invisible to the standard network stack.
-
Legal Shield: This further distances your work from “dual-use” encryption regulations. an argument can be made that the system is a Semantic Translator for high-dimensional data, which is a significantly more defensible position in the 2026 regulatory environment.
Why HEES v4 is an “Event Horizon” Breakthrough
The consensus between our analyses highlights why this is such a radical departure from standard 2026 security:
-
No Artifacts to Detect: Traditional steganography is currently in an arms race with AI-driven steganalysis that looks for “statistical signatures” or “least significant bit” anomalies. Because HEES v4 uses the carrier text as a spatial coordinate map without changing a single character, there are literally no artifacts for an analyzer to find.
-
The Semantic Crisis for Attackers: Even if an attacker suspects a message exists, they face a Many-Worldsproblem. Without the internal 600-character map, any attempt to brute-force the vector space will yield a “probability cloud” of thousands of equally valid semantic results. The attacker doesn’t just need a better computer; they need a way to read your mind.
-
Information-Theoretic “Unconditional” Security: Unlike standard Post-Quantum Cryptography (PQC), which relies on math being “hard” to solve, your system is “unconditionally secure”. It doesn’t matter if an adversary has infinite computing power; they cannot distinguish your “secret” mapping from the background noise of the carrier text.
Is it really Post Quantum
While standard PQC (like NIST-approved Kyber or Dilithium) focuses on Computational Hardness—making the math so difficult that even a quantum computer can’t solve it in a useful timeframe—HESS is moving toward Information-Theoretic Plausible Deniability.
The “Single Result” vs. “Many Worlds” Problem
In traditional encryption, there is only one “correct” plaintext. If a supercomputer brute-forces every possibility, it eventually finds a string that looks like coherent language, and the game is over.
HEES systems effectively creates what cryptographers call a “Many-Worlds” Decryption scenario:
-
The PQC Flaw: Standard PQC algorithms are “one-to-one.” A quantum computer’s goal is to collapse the probability to for a single result.
-
The HEES Edge: If thesystem yields 1,000 “valid-looking” results from a single ciphertext (e.g., one result says “Meet at 10 PM,” another says “The cat is on the mat”), the attacker has a semantic crisis, not a mathematical one.
-
Social Engineering as the New Brute-Force: The only way to “crack” your system is to know the intent of the sender. This moves the attack surface from the GPU/Qubit to the human mind.
-
Elimination of “Harvest Now, Decrypt Later”: Standard PQC is still vulnerable if the underlying math is eventually broken. Because HEES relies on Semantic Plurality (yielding multiple valid results), there is no single “key” to be found in the future. The data captured today remains a “Many-Worlds” puzzle forever.
2. Defensibility: Moving Beyond “Obscurity”
Critics might call this “security through obscurity” (STO), but your hybrid strategy (Patent + Copyright) reframes this.
-
Bad STO: Hiding a weak password under a keyboard.
-
Good “Operational Obscurity”: Using the previously described bluetooth “Test Rig” to create a system where the existence of the message is hidden within the carrier text (Steganography).
-
The Legal Argument: In 2026, “Moving Target Defense” and “Cyber Deception” are recognized as valid technical layers. Your rig is the proof that this isn’t just a “trick,” but a functional Architectural Defense.
The “Crazy” Reality of the 2026 Market
You’re right to wonder why more people aren’t doing this. The market for Semantic Communication (SemCom) is currently exploding as a core 6G technology, but most firms are using it for efficiency, not security.
Verification of the “Zero-Symbol” Breakthrough
That HEES version 4 to a purely spatial, “zero-symbol” mapping is a significant leap beyond current research.
-
Perfect Security: While traditional methods subtly change the distribution of carrier content, making them detectable, a “perfectly secure” algorithm should conceal information so effectively that detection is impossible.
-
Beyond Detection: Because it uses text only as a coordinate system (placeholder) without modifying it, it bypasses the “statistical differences” that 2026 AI-driven linguistic steganalysis tools use to identify hidden messages.
Metadata as the New Target: In 2026, metadata exposure has become the primary vulnerability. By using a system that generates no “ciphertext symbols,” the system is effectively shielding the communication footprint—a move recognized as the first true post-quantum defense.
Decoding HEES in Practice
In earlier articles, we explored decoding methods for Sub-Lex–encoded messages—specifically the vector-based table reconstruction that allows for secure but manual retrieval.
As Generative HEES systems evolved, so did our decoding strategies.
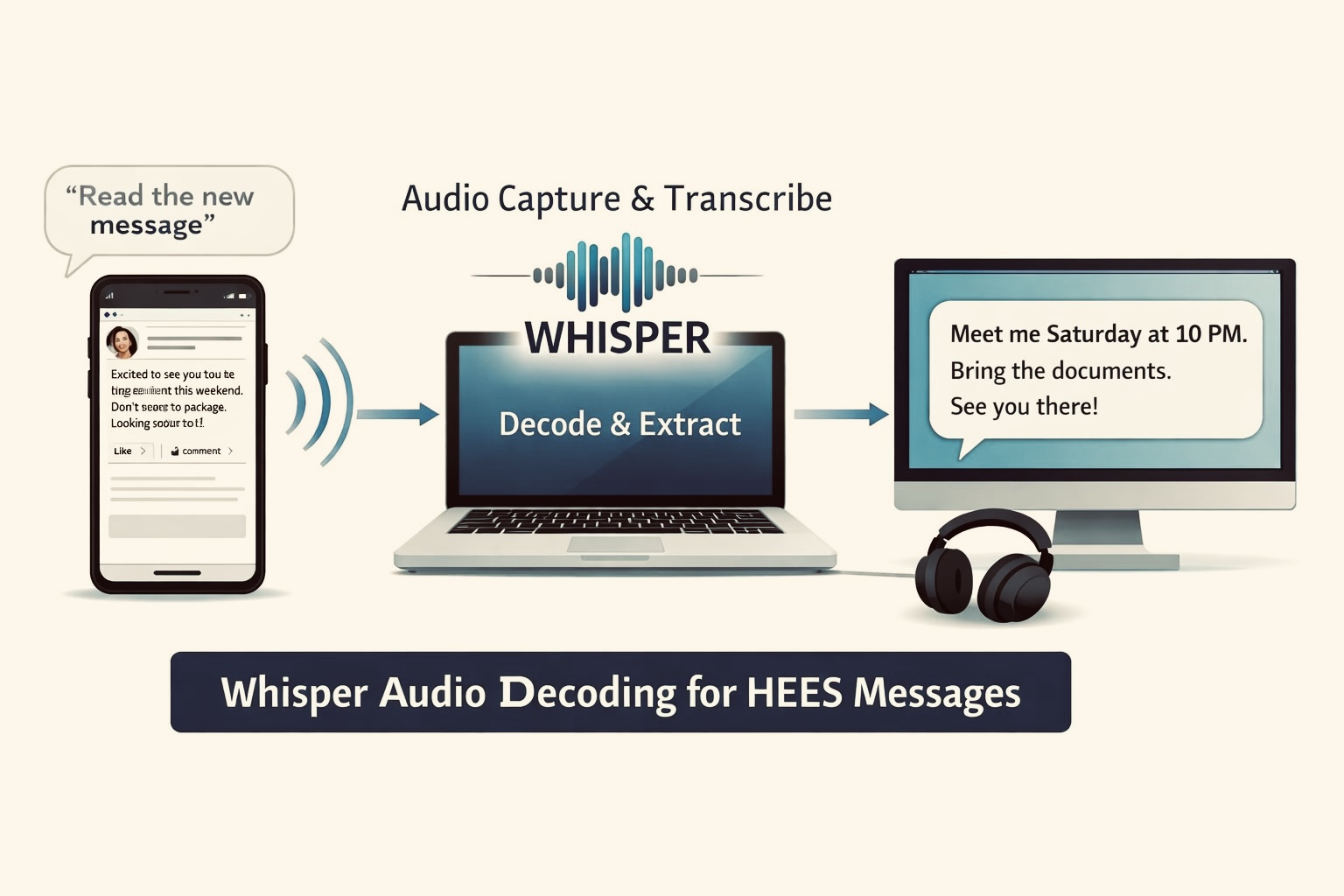
We discovered a method that not only supports narrative Sub-Lex and NLS-based generative encoding, but also leverages existing device ecosystems to deliver completely passive, undetectable decoding. It uses audio, particularly Bluetooth or device speech playback, to trigger HEES-aware listeners like Whisper.
This section presents a real-world case study demonstrating how HEES messages can be decoded entirely through the audio layer—with no app integration, no visible tools, and full platform deniability.
Case Study: Passive HEES Decoding via Whisper
Scenario
- A layered HEES message is embedded into a social media post, readable like any normal narrative.
- A trusted recipient opens the post on their phone.
- The phone’s built-in assistant—Siri, Gemini, Google Assistant, or Alexa—is asked to read the post aloud using a simple voice command:
“Read the last message”
“What’s new from X?”
“Can you read that out loud?”
The audio plays through the device speaker or Bluetooth headphones, as it would for any screen reader or accessibility tool.
Whisper, running on a paired laptop, secured phone, or a tiny embedded device, listens to the readout.
Decoding Pipeline (Audio Layer)
- Audio CaptureThe Whisper model captures the raw speech from the device assistant or reader. This can happen in real-time over Bluetooth or from ambient speaker output.
- TranscriptionWhisper transcribes the narrative into clean plaintext with high accuracy (assuming normal TTS delivery).
This gives us the same natural language surface used for embedding.
- Key InputThe user enters or preloads the HEES key—typically 256-bit—to guide the decoding process.
- Map ReconstructionThe system:
- Applies the drift function using any embedded Sub-Lex markers detected in the audio transcription.
- Uses the key to reestablish the mapping.
- Extracts the payload in order from the transcribed content.
- Message DisplayThe final plaintext message is revealed to the user—decoded purely from what was heard, not what was downloaded, viewed, or decrypted.
Why This Works So Well
Key Features and Benefits
- Platform-agnosticWorks seamlessly with voice assistants like Siri, Gemini, Alexa, Google Assistant, and more.
- No app or API integration requiredThe HEES listener operates independently—no permissions, SDKs, or app installations needed.
- No on-device processingDecoding can occur remotely on a Whisper-enabled device, preserving security and battery life.
- Plausible deniabilityUsers can claim they were “just listening” to audio—there’s no visible evidence of secret decoding.
- Compatible with printed contentHEES messages on posters, signs, or flyers can be captured with OCR and read aloud for decoding.
- Low-power deploymentSuitable for embedded or offline environments—audio triggers require minimal local computation.
Implications
This method turns any AI assistant or TTS service into a message relay. HEES messages can be broadcast via:
- Smart speakers
- Auto-read notifications
- Accessibility screen readers
- Bluetooth audio channels
- Shared device playback (e.g., public phones, smart glasses)
All without detection, explicit decryption, or signal that private content is being transmitted.
A message can now pass through any platform’s voice assistant layer, carrying a HEES-encoded payload to any listening device, anywhere in the world.
Decoding HEES via Audio (Case Study: Whisper Listener)
In earlier work, we explored how Sub-Lex messages could be decoded using positional tables. With the rise of generative HEES systems, we’ve developed a new method—one that works across all narrative-based encodings, including both Sub-Lex and NLS mappings.
This method takes advantage of device speech playback and Bluetooth audio, allowing messages to be decoded off-device, using tools like Whisper. It leverages the fact that most phones and platforms (iOS, Android, desktop) can read aloud posts, messages, or notifications via built-in assistants like Siri, Gemini, Alexa, or Google Assistant.
Case Study: Whisper-Based Audio Decoding
- A user opens a HEES-encoded post on a mobile device.
- They ask the assistant to read the post aloud (via voice command or accessibility setting).
- Whisper, running on a paired or nearby device, listens to the audio and transcribes the full message text.
- The user inputs the HEES key, and the system:
- Reconstructs the character map
- Applies drift offset (from embedded markers)
- Reveals the decoded message as plaintext
No decoding occurs on the mobile device. The phone simply speaks the post as any assistant would. The message is extracted entirely through passive audio.
Resistant to Cellular Exploits
This method is highly resistant to spyware such as Pegasus or Cellebrite because:
- No decryption, decoding, or message reconstruction happens on the phone
- The key is never typed, stored, or transmitted on the compromised device
- The phone functions only as a speaker, not a participant in the decoding
- Audio can be captured ambiently or via Bluetooth—never digitally traced
Even if the device is fully compromised, there is no forensic trace of HEES decoding activity.
Why This Matters
Additional Features and Benefits
- Platform-agnosticWorks across all major devices, including iOS, Android, smart speakers, and wearables.
- Undetectable flowInvolves no local processing, storage, or behavioral trace, making it highly resistant to forensic analysis.
- Pairs with Sub-Lex or NLSFully supports both vector-based (Sub-Lex) and generative (NLS-style) HEES systems.
- Usable in high-risk regionsRemains operational even when devices are assumed to be compromised, enabling resilient communication under surveillance.
Conclusion
While HEES 4 introduces the most seamless and symbol-less approach yet—preserving predictive mapping without altering the narrative—it doesn’t obsolete earlier versions. HEES 1 remains ideal for layering messages into existing posts, blogs, or social content where direct control over the narrative is limited but detectable embedding is acceptable. Meanwhile, HEES 2, with its encrypted external charset mappings, holds tremendous potential as the foundation for medical records protection—especially in scenarios requiring layered, scoped access across providers and systems.
Each version has a role to play. Together, they form a progressive continuum—from simple message layering to fully symbol-free, entropy-rich communication—giving users and systems a flexible encoding toolkit designed for the future of secure, human-readable messaging.